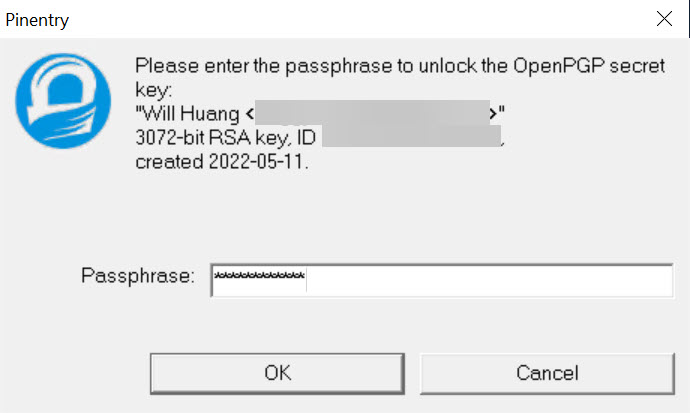
When we are going to transfer confidential files, we may face many different transmission methods, but the process must ensure information security, so you will need to consider many factors. In this article, I intend to share how to use the GPG tool to sign and encrypt files. No matter the file is sent to the other party by any means, only a clearly specified object can open the file, so as to achieve the confidentiality of information security (Confidentiality) And integrity (Integrity) requirements.
… continue reading …
This article is reprinted from https://blog.miniasp.com/post/2022/05/11/gnupg
This site is for inclusion only, and the copyright belongs to the original author.